Cryptography is the invisible backbone of your business
Every time a member of your team sends an email, logs into a cloud platform, processes a payment or connects via Virtual Private Network (VPN), a cryptographic algorithm is working silently in the background to secure that activity. You probably never think about it. Most Small and Medium-sized Enterprise (SME) owners do not. But that invisible layer of protection is now under serious threat. The algorithms doing this work, Rivest-Shamir-Adleman (RSA) and Elliptic Curve Cryptography (ECC) have protected digital communications for decades. They work because the math behind them is too hard for any classical computer to crack in a useful timeframe. Quantum computers solve that math differently. And they are being built right now.
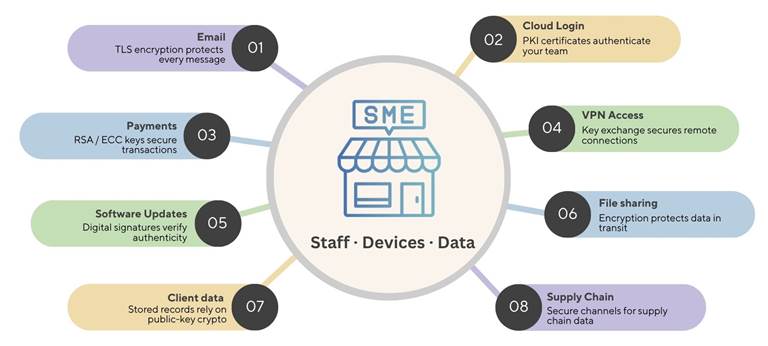
Every digital activity in your SME depends on encryption and that encryption is at risk.
The attack has already started
This is not a future risk sitting safely on the horizon. Intelligence agencies across multiple countries are warning that adversaries are already collecting encrypted business data today, storing it and waiting for quantum computers powerful enough to decrypt it. The attack has a name in the security community: Harvest Now, Decrypt Later (HNDL). The contracts, client records and financial data your business sends today could already be sitting in an adversary’s storage which is encrypted, unreadable for now but waiting to be decrypted the moment a quantum computer powerful enough becomes available to break today’s encryption.
The transition window is narrowing
The conservative planning assumption is that a cryptographically relevant quantum computer will exist between 2030 and 2035. A full migration to quantum-safe cryptography takes two to five years for most organizations. The question is no longer whether to make this transition. For SMEs, it comes down to three things: how to do it, when to start and what it will cost to get there without disruption.
The new standards are already here
In August 2024, the National Institute of Standards and Technology (NIST) published the first three finalized post-quantum cryptography standards; ML-KEM, ML-DSA and SLH-DSA. These new algorithms are designed to be secure against both classical and quantum adversaries and are available for deployment today.
Why now? The regulatory clock is already running
The UK’s National Cyber Security Centre (NCSC) has published a clear phased migration roadmap with three target dates: Discover and Plan by 2028, Prioritise and Pilot from 2028 to 2031 and Complete Adoption from 2031 to 2035. For SMEs in finance, legal, insurance, healthcare or any regulated sector, these timelines will flow directly into procurement requirements and supply chain contracts. Larger clients and regulated institutions will increasingly require evidence of cryptographic readiness from their partners and suppliers.
Eligibility, not just security
Beginning now is not only about protecting your data. It is about continued eligibility to operate within the supply chains of the larger, regulated organisations you serve. The businesses that cannot demonstrate PQC readiness will find themselves excluded from contracts before a single quantum computer has been used against them.
Your supply chain is your biggest vulnerability
Large enterprises have dedicated security teams. Governments have mandates and budgets. SMEs sit in the middle relying on third-party software vendors, cloud platforms, managed service providers and Software as a Service (SaaS) tool while supplying services upward to larger clients. Every link in that chain uses cryptography. Every link is therefore a potential point of quantum-era vulnerability. Up to 40% of cyber threats now occur indirectly through the supply chain (AAG IT, The Latest Cyber Crime Statistics, 2025). A compromised software library, an outdated certificate from a cloud provider or vulnerable firmware in a network device can cascade across every organisation that depends on it.

Most SMEs have no visibility into their supply chain risk
Only 14% of UK businesses and 9% of charities assessed supply chain cyber risks in 2025 despite supply chains being a recognised major vulnerability (UK Government, Cyber Security Breaches Survey 2025, Department for Science, Innovation and Technology, 2025). Many SMEs are already running quantum-vulnerable cryptography without knowing it, embedded in a vendor SDK, a managed cloud service or network device firmware that has never been audited. Third-party supply chain breaches now account for 30% of all data breaches globally, double the rate of the previous year (Verizon, Data Breach Investigations Report, 2025).The average cost of the most disruptive cyber-attack on a medium-sized UK business reached £10,830 in 2024 (UK Government, Cyber Security Breaches Survey 2024, DSIT, 2024). That figure does not yet include the deferred liability of harvested data waiting to be decrypted.
What you control and what your vendors must deliver
Much of the heavy cryptographic work, replacing algorithms inside operating systems, browsers, cloud platforms and enterprise software will be carried out by your technology vendors. For SMEs using standard commodity IT, much of that migration will happen seamlessly as services are updated (NCSC, Timelines for Migration to Post-Quantum Cryptography, 2025). But this does not make SMEs passive. There is a set of high-value actions entirely within your control and the timing of those actions determines whether your business absorbs manageable, planned costs or faces a compressed, expensive scramble.
Actions within your direct control
- Conduct a cryptographic inventory to understand where your business relies on public-key encryption
- Review your key vendors’ PQC roadmaps and confirm alignment with NIST FIPS 203, 204 and 205 standards
- Minimise long-term storage of sensitive encrypted data to reduce HNDL exposure
- Ensure software and firmware updates are applied promptly as quantum-safe versions become available
- Manage your certificates actively as hybrid PQC certificates are beginning to enter production environments
Actions that require vendor coordination
- The actual algorithm replacement inside third-party platforms and managed services
- Hardware security module and firmware certification updates, which require extensive evaluation often resulting in multi-year certification cycles (NCSC, Timelines for Migration to PQC, 2025)
- Protocol-level changes in TLS, SSH and VPN infrastructure, though major providers including Google and Cloudflare have already begun deploying hybrid quantum-safe key exchanges
Understanding this split is critical for budgeting. Not everything needs to be done at once. Much of the heaviest technical lifting will happen on vendor roadmaps but you need to be actively tracking and requesting it.
The SME quantum security checklist
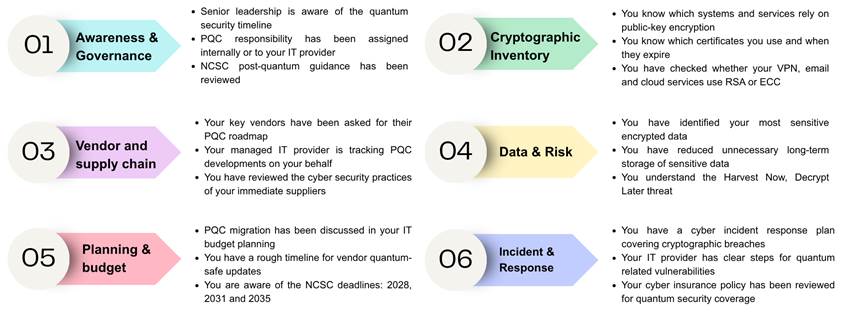
Use this checklist to assess where your business stands today. It covers five areas aligned to NCSC guidance and is designed specifically for UK SMEs at the start of their PQC journey.
Cost and benefit: Why is acting now cheaper than waiting
At Zhero, we work with SMEs every day and we understand that every budget decision needs a clear business case. The question we hear most often is: do we really need to spend money on this now, when quantum computers do not fully exist yet? The honest answer is YES.
The cost of planning versus the cost of reacting
A planned migration spread across five years is a manageable IT cost. It sits alongside your existing refresh cycles and vendor renewals with no single large bill. Each year builds on the last and most of the work simply means having the right conversations with vendors you already work with. The alternative is not free. Waiting means arriving at a deadline or worse, a breach with no plan, no inventory and no preparation. At that point the same work costs far more, done in a rush with emergency fees and compliance gaps to fix on top.
The deferred liability no other cyber risk carries
Unlike conventional cyber risks, the quantum threat carries a deferred liability, data your business has already sent or stored may have been harvested and is waiting to be decrypted. Reducing long-term storage of sensitive data now is one of the few actions that addresses exposure that has already occurred, and it costs very little to act on.
What the numbers show
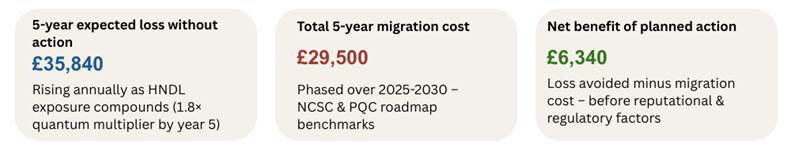
For a typical UK SME, the five-year expected loss from inaction (£35,840) already exceeds the total cost of a planned five-year migration (£29,500) even before regulatory fines and reputational damage are considered. Planning now is not a large investment. Not planning is.
Your five-year transition roadmap
The roadmap below outlines the five phases of your PQC transition, aligned to the NCSC’s migration timeline.
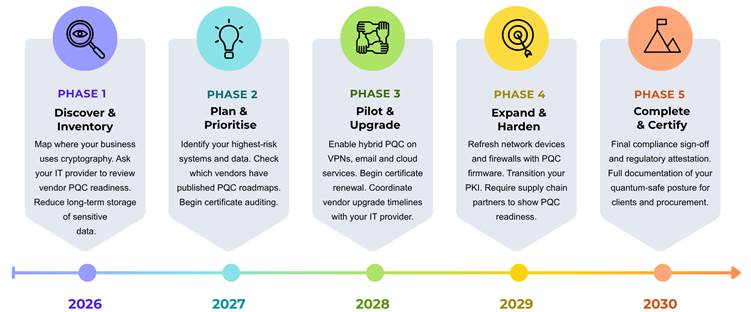
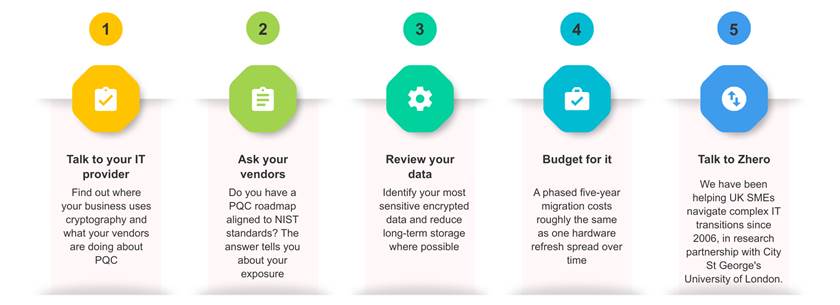
Next steps: where to start
Post-quantum cryptography is no longer a distant or purely technical concern. For SMEs it is a practical planning issue shaped by supply chain dependencies, regulatory timelines and long-term data risk. The businesses that start now will spread their costs, stay ahead of procurement requirements and avoid the scramble that comes with leaving it too late.
Five actions you can take this month
The longer you wait, the more it costs
The transition to post-quantum security is inevitable. The advantage lies with those who approach it as a planned investment rather than a last-minute response. The quantum clock is already ticking. The question is simply whether your business is ready when it goes off.





